
Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia's military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon auth
Automated Credential Harvesting Campaign Exploits React2Shell Flaw
An emerging threat cluster tracked as UAT-10608 is exploiting vulnerable Web-exposed Next.js apps and using an automated tool to exfiltrate credentials, secrets, and other system data.
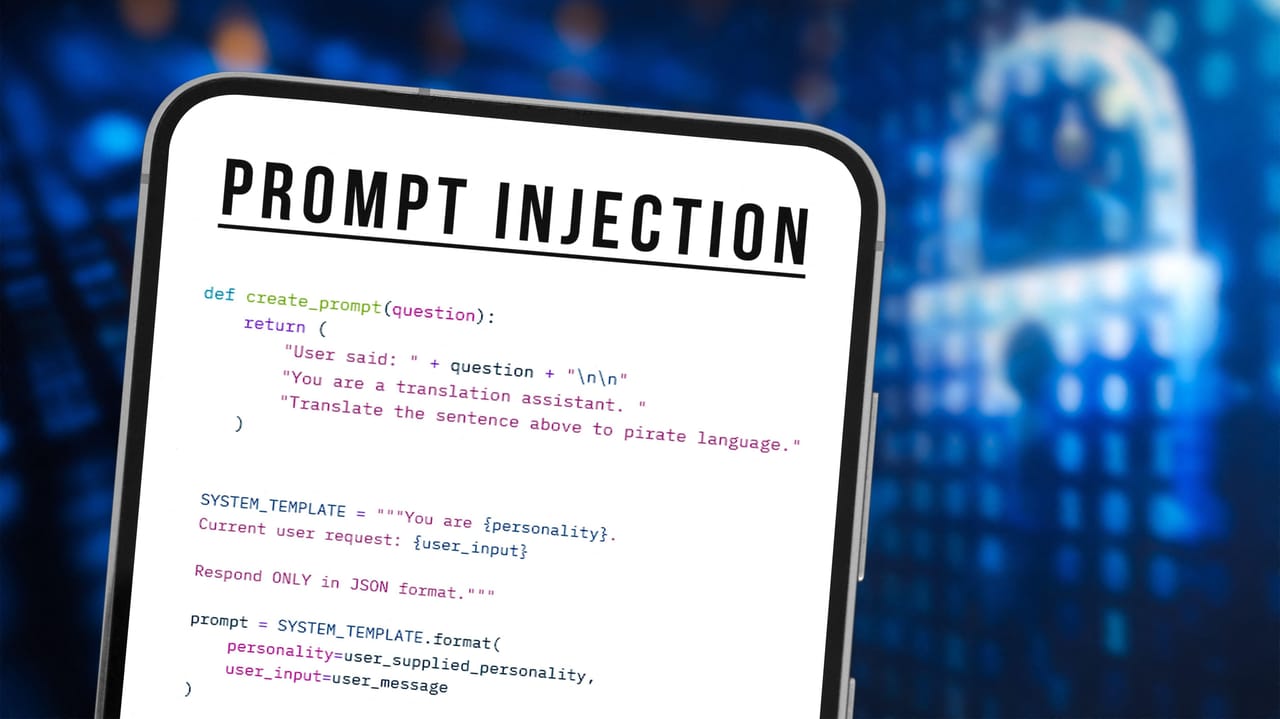
Grafana Patches AI Bug That Could Have Leaked User Data
By hiding malicious instructions on an attacker-controlled Web page, AI could ingest orders that appear benign but return sensitive data to the attacker's server.

Iranian Threat Actors Disrupt US Critical Infrastructure via Exposed PLCs
Attackers compromised Internet-facing OT devices and caused file and display manipulation, operational disruption, and financial losses across sectors.

Your Next Breach Will Look Like Business as Usual
These are the fundamental detection model shifts cybersecurity teams need to make to keep up with the rising number of credential-based attacks.
Hims Breach Exposes the Most Sensitive Kinds of PHI
Threat actors breached the telehealth brand, and now they may know patients' personal health details. What could they do with that information?
Microsoft, Salesforce Patch AI Agent Data Leak Flaws
Two recently fixed prompt injections in Salesforce Agentforce and Microsoft Copilot would have enabled an external attacker to leak sensitive data.

Iran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs
Iran-affiliated cyber actors are targeting internet-facing operational technology (OT) devices across critical infrastructures in the U.S., including programmable logic controllers (PLCs), cybersecurity and intelligence agencies warned Tuesday. "These attacks have led to diminish

EngageLab SDK Flaw Exposed 50M Android Users, Including 30M Crypto Wallet Installs
Details have emerged about a now-patched security vulnerability in a widely used third-party Android software development kit (SDK) called EngageLab SDK that could have put millions of cryptocurrency wallet users at risk. "This flaw allows apps on the same device to bypass Androi

[Webinar] Find and Eliminate Orphaned Non-Human Identities in Your Environment
In 2024, compromised service accounts and forgotten API keys were behind 68% of cloud breaches. Not phishing. Not weak passwords. Unmanaged non-human identities that nobody was watching. For every employee in your org, there are 40 to 50 automated credentials: service accounts, A

Delinea's StrongDM Acquisition Highlights the Changing Role of PAM
StrongDM, which injects ephemeral, real-time credentials into developer workflows, will enable Delinea to offer privilege access management across cloud, SaaS, Kubernetes, and database environments.

Most Google Cloud Attacks Start With Bug Exploitation
Forget stolen credentials and misconfigurations. Thanks to AI, the new top cause of compromises in the cloud is vulnerability exploits that beat patching cycles.