
JanelaRAT: a financial threat targeting users in Latin America
Kaspersky GReAT experts describe the latest JanelaRAT campaign detailing infection chain and malware functionality updates.
Threat landscape for industrial automation systems in Q4 2025
The report contains industrial threat statistics for Q4 2025. It covers various infection vectors and malware types, as well as regional statistics and statistics by industry.

Weaponizing the Protectors: TeamPCP’s Multi-Stage Supply Chain Attack on Security Infrastructure
TeamPCP continues its string of supply chain attacks, and announces a partnership with Vect ransomware group. The post Weaponizing the Protectors: TeamPCP’s Multi-Stage Supply Chain Attack on Security Infrastructure appeared first on Unit 42.
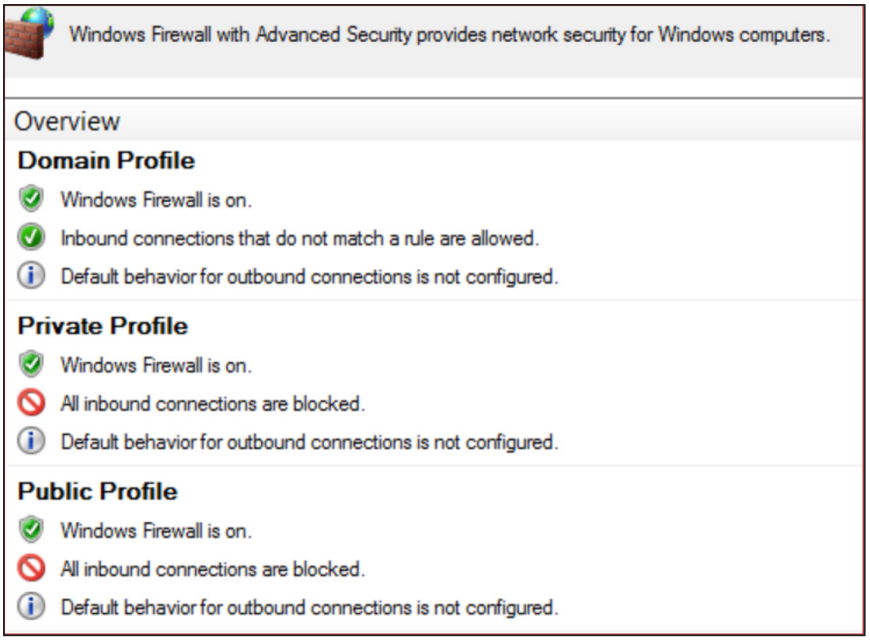
Proactive Preparation and Hardening Against Destructive Attacks: 2026 Edition
Written by: Matthew McWhirt, Bhavesh Dhake, Emilio Oropeza, Gautam Krishnan, Stuart Carrera, Greg Blaum, Michael Rudden UPDATE (March 13): Added guidance around abuse or misuse of endpoint / MDM platforms. Background Threat actors leverage destructive malware to destroy data, el

Ransomware Under Pressure: Tactics, Techniques, and Procedures in a Shifting Threat Landscape
Written by: Bavi Sadayappan, Zach Riddle, Ioana Teaca, Kimberly Goody, Genevieve Stark Introduction Since 2018, when many financially motivated threat actors began shifting their monetization strategy to post-compromise ransomware deployments, ransomware has become one of the m

Feds Disrupt IoT Botnets Behind Huge DDoS Attacks
The U.S. Justice Department joined authorities in Canada and Germany in dismantling the online infrastructure behind four highly disruptive botnets that compromised more than three million hacked Internet of Things (IoT) devices, such as routers and web cameras. The feds say the

‘CanisterWorm’ Springs Wiper Attack Targeting Iran
A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran's time zone or have Farsi set as the default language.

'BlackSanta' EDR Killer Targets HR Workflows
A campaign by Russian-speaking cyberattackers hijacks workflows to deliver security-busting malware, allowing attackers to steal data without detection.

Russian Threat Actor Sednit Resurfaces With Sophisticated Toolkit
After several years of using simple implants, the Russia-affiliated actor is back with two new sophisticated malware tools.

INC Ransomware Group Holds Healthcare Hostage in Oceania
Government agencies, emergency clinics, and others in Australia, New Zealand, and Tonga have had serious run-ins with the prolific ransomware outfit.

Real-Time Banking Trojan Strikes Brazil's Pix Users
The latest banking Trojan campaign to hit Brazil combines classic malware with a real-time human operator, waiting for the perfect moment to strike.

GlassWorm Malware Evolves to Hide in Dependencies
Dozens of updated, malicious GlassWorm extensions have infested Open VSX, threatening software development supply chains.