
AI-Assisted Supply Chain Attack Targets GitHub
PRT-scan is the second campaign in recent months where a threat actor appears to have leveraged AI for automated targeting of a widespread GitHub misconfiguration.
Focusing on the People in Cybersecurity at RSAC 2026 Conference
AI dominated RSAC 2026 Conference, but it's still the humans in cybersecurity who matter most.

Lies, Damned Lies, and Cybersecurity Metrics
A panel of five C-suite leaders discuss how cybersecurity success is measured and why it isn't improving results.
Human vs. AI: Debates Shape RSAC 2026 Cybersecurity Trends
As AI dominated RSAC 2026, CISOs and industry leaders debated its role in security, from agentic applications to the challenges of scaling human involvement in decision-making.

RSAC 2026: How AI Is Reshaping Cybersecurity Faster Than Ever
Dark Reading's Kelly Jackson Higgins shares insights on the past, present, and future of cybersecurity after attending RSAC 2026 Conference.
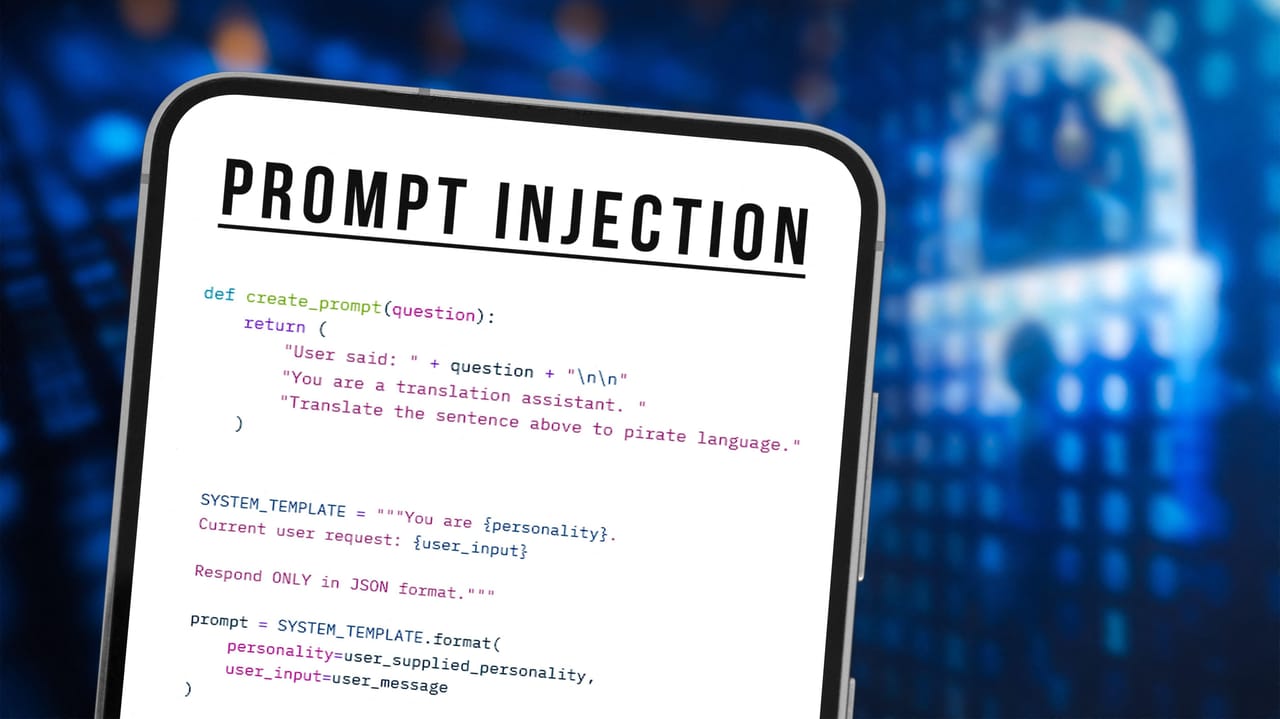
Grafana Patches AI Bug That Could Have Leaked User Data
By hiding malicious instructions on an attacker-controlled Web page, AI could ingest orders that appear benign but return sensitive data to the attacker's server.

Storm-1175 Deploys Medusa Ransomware at 'High Velocity'
Microsoft says the financially motivated cybercrime group has exploited n-day and zero-day vulnerabilities in campaigns predicated on speed.

Iranian Threat Actors Disrupt US Critical Infrastructure via Exposed PLCs
Attackers compromised Internet-facing OT devices and caused file and display manipulation, operational disruption, and financial losses across sectors.

Pluralsight Launches SecureReady to Help Organizations Build Job-Ready Cybersecurity Teams

Full Sail University to Open IBM Cyber Defense Range Powered by AWS and Cloud Range on Campus

Fraud Rockets Higher in Mobile-First Latin America
Cyber-fraudsters move quickly from compromised devices to account takeover to funds transfer, shifting money before many financial institutions can react.