
Healthy Security Cultures Want People to Report Risks
The signs of an effective security culture are shifting as companies call on CISOs and security teams to raise their hands unabashedly.
_Cagkan_Sayin_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale)
Europe's GCVE Raises Concerns Over Fragmentation in Vulnerability Databases
GCVE would enhance global collaboration, flexibility, and efficiency in tracking security flaws. Duplicate entries and a decentralization policy may create more chaos for defenders.

Exploited Zero-Day Flaw in Cisco UC Could Affect Millions
Mass scanning is underway for CVE-2026-20045, which Cisco tagged as critical because successful exploitation could lead to a complete system takeover.
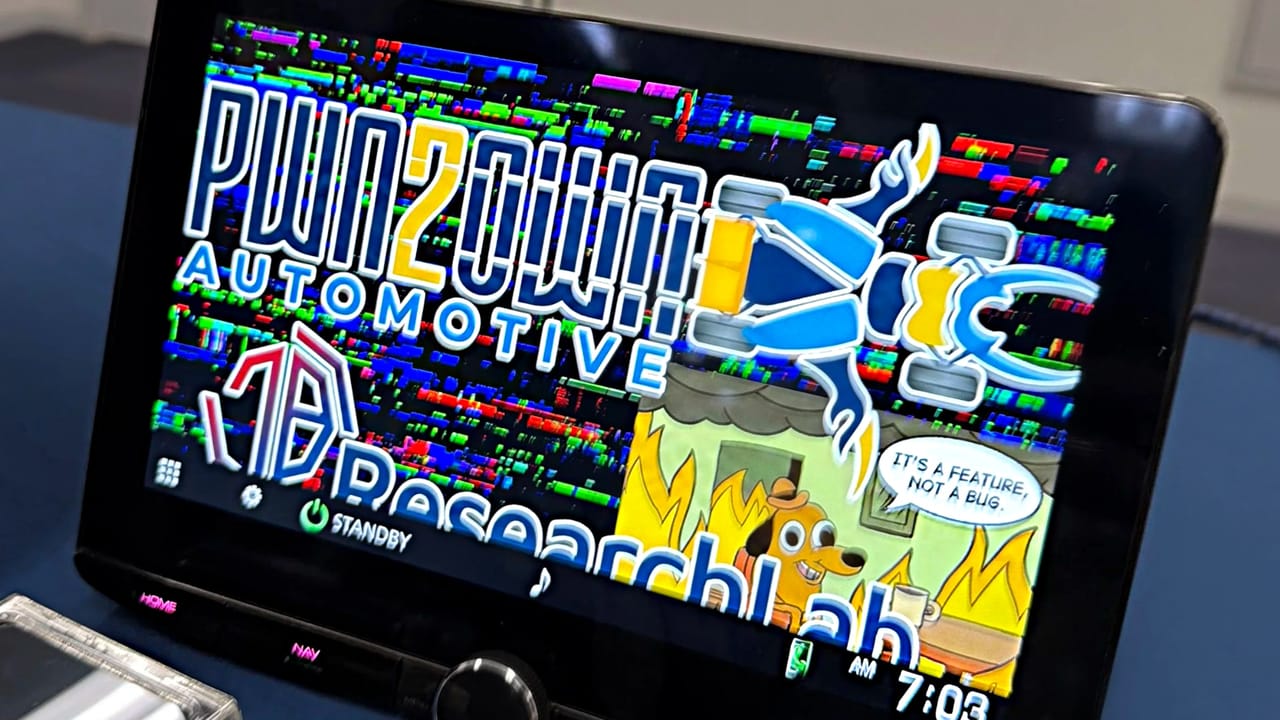
Swipe, Plug-in, Pwned: Researchers Find New Ways to Hack Vehicles
Security researchers exploited dozens of vulnerabilities in vehicle infotainment systems and EV chargers during the latest Pwn2Own contest at Automotive World 2026.

2025 Was a Wake-up Call to Protect Human Decisions, Not Just Systems
Cybersecurity must shift from solely protecting systems to safeguarding human decision-making under uncertainty and system failures.

DPRK's Konni Targets Blockchain Developers With AI-Generated Backdoor
The North Korean threat group is using a new PowerShell backdoor to compromise development environments and target cryptocurrency holdings, according to researchers.

Sandworm Blamed for Wiper Attack on Poland Power Grid
Researchers attributed the failed attempt to the infamous Russian APT Sandworm, which is notorious for wiper attacks on critical infrastructure organizations.

Beauty in Destruction: Exploring Malware's Impact Through Art
Artistic initiatives turn cybersecurity into immersive exhibits at the Museum of Malware Art, transforming digital threats into thought-provoking experiences.

Hand CVE Over to the Private Sector
How MITRE has mismanaged the world's vulnerability database for decades and wasted millions along the way.

WorldLeaks Extortion Group Claims It Stole 1.4TB of Nike Data
The sportswear brand is investigating an alleged breach of its network that exposed some 188,347 files of highly sensitive corporate data.

'Stanley' Toolkit Turns Chrome Into Undetectable Phishing Vector
The malware-as-a-service kit enables malicious extensions to overlay pages on real websites without changing the visible URL, signaling a fresh challenge for enterprise security.

Microsoft Rushes Emergency Patch for Office Zero-Day
To exploit the vulnerability, an attacker would need either system access or be able to convince a user to open a malicious Office file.