
Keys to the Kingdom: A Defender's Guide to Privileged Account Monitoring
Written by: Bhavesh Dhake, Will Silverstone, Matthew Hitchcock, Aaron Fletcher The Criticality of Privileged Access in Today's Threat Landscape Privileged access stands as the most critical pathway for adversaries seeking to compromise sensitive systems and data. Its protection

Preparing for Threats to Come: Cybersecurity Forecast 2026
Every November, we make it our mission to equip organizations with the knowledge needed to stay ahead of threats we anticipate in the coming year. The Cybersecurity Forecast 2026 report, released today, provides comprehensive insights to help security leaders and teams prepare fo

GTIG AI Threat Tracker: Advances in Threat Actor Usage of AI Tools
Executive Summary Based on recent analysis of the broader threat landscape, Google Threat Intelligence Group (GTIG) has identified a shift that occurred within the last year: adversaries are no longer leveraging artificial intelligence (AI) just for productivity gains, they are d

No Place Like Localhost: Unauthenticated Remote Access via Triofox Vulnerability CVE-2025-12480
Written by: Stallone D'Souza, Praveeth DSouza, Bill Glynn, Kevin O'Flynn, Yash Gupta Welcome to the Frontline Bulletin Series Straight from Mandiant Threat Defense, the "Frontline Bulletin" series brings you the latest on the threats we are seeing in the wild right now, equippin

Time Travel Triage: An Introduction to Time Travel Debugging using a .NET Process Hollowing Case Study
Written by: Josh Stroschein, Jae Young Kim The prevalence of obfuscation and multi-stage layering in today’s malware often forces analysts into tedious and manual debugging sessions. For instance, the primary challenge of analyzing pervasive commodity stealers like AgentTesla is

Frontline Intelligence: Analysis of UNC1549 TTPs, Custom Tools, and Malware Targeting the Aerospace and Defense Ecosystem
Written by: Mohamed El-Banna, Daniel Lee, Mike Stokkel, Josh Goddard Overview Last year, Mandiant published a blog post highlighting suspected Iran-nexus espionage activity targeting the aerospace, aviation, and defense industries in the Middle East. In this follow-up post, Mand

Beyond the Watering Hole: APT24's Pivot to Multi-Vector Attacks
Written by: Harsh Parashar, Tierra Duncan, Dan Perez Google Threat Intelligence Group (GTIG) is tracking a long-running and adaptive cyber espionage campaign by APT24, a People's Republic of China (PRC)-nexus threat actor. Spanning three years, APT24 has been deploying BADAUDIO,

Sanctioned but Still Spying: Intellexa’s Prolific Zero-Day Exploits Continue
Introduction Despite extensive scrutiny and public reporting, commercial surveillance vendors continue to operate unimpeded. A prominent name continues to surface in the world of mercenary spyware, Intellexa. Known for its “Predator” spyware, the company was sanctioned by the US

Multiple Threat Actors Exploit React2Shell (CVE-2025-55182)
Written by: Aragorn Tseng, Robert Weiner, Casey Charrier, Zander Work, Genevieve Stark, Austin Larsen Introduction On Dec. 3, 2025, a critical unauthenticated remote code execution (RCE) vulnerability in React Server Components, tracked as CVE-2025-55182 (aka "React2Shell"), was
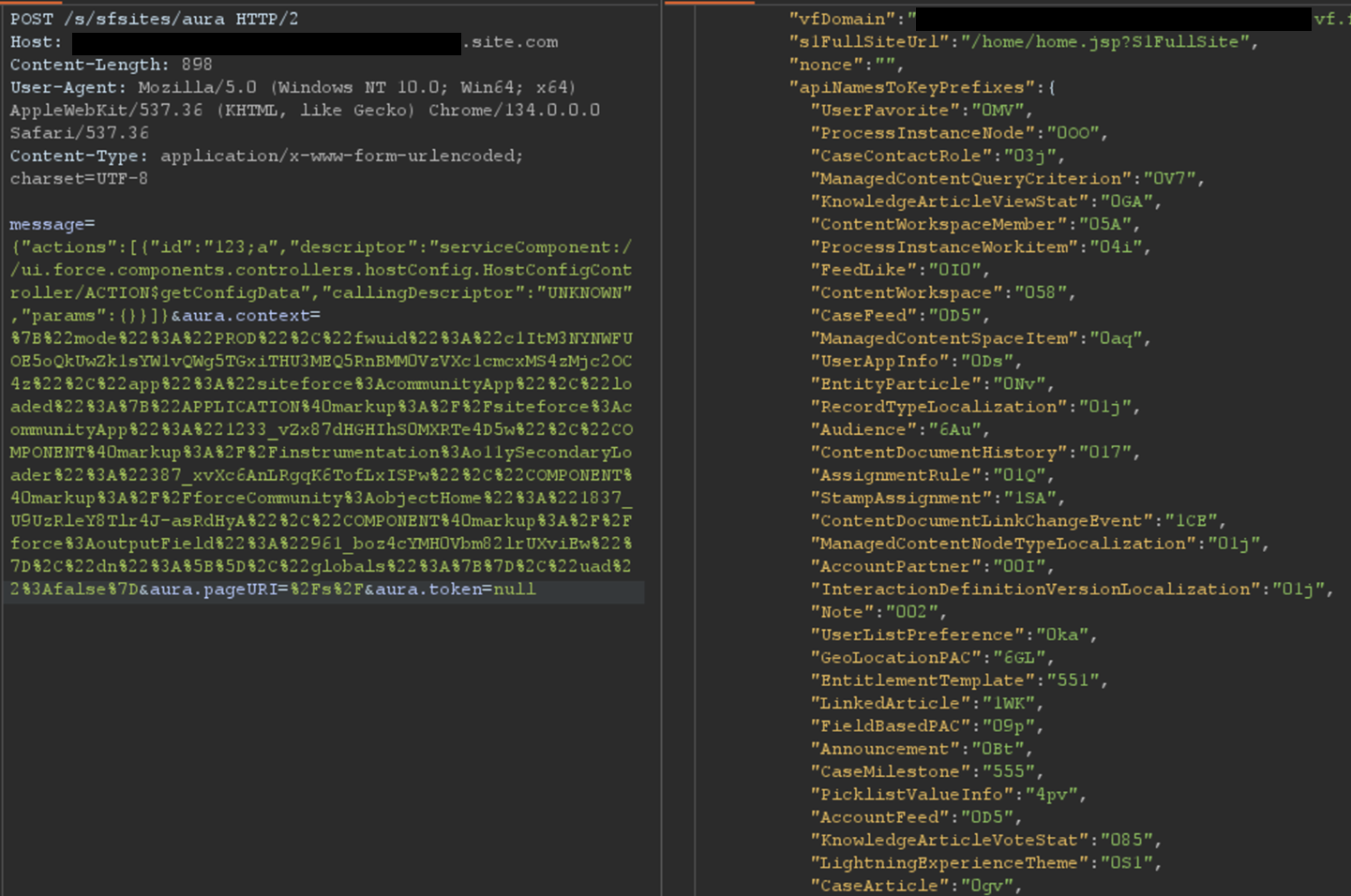
AuraInspector: Auditing Salesforce Aura for Data Exposure
Written by: Amine Ismail, Anirudha Kanodia Introduction Mandiant is releasing AuraInspector, a new open-source tool designed to help defenders identify and audit access control misconfigurations within the Salesforce Aura framework. Salesforce Experience Cloud is a foundational

Closing the Door on Net-NTLMv1: Releasing Rainbow Tables to Accelerate Protocol Deprecation
Written by: Nic Losby Introduction Mandiant is publicly releasing a comprehensive dataset of Net-NTLMv1 rainbow tables to underscore the urgency of migrating away from this outdated protocol. Despite Net-NTLMv1 being deprecated and known to be insecure for over two decades—with

Meet Rey, the Admin of ‘Scattered Lapsus$ Hunters’
A prolific cybercriminal group that calls itself "Scattered LAPSUS$ Hunters" made headlines regularly this year by stealing data from and publicly mass extorting dozens of major corporations. But the tables seem to have turned somewhat for "Rey," the moniker chosen by the technic