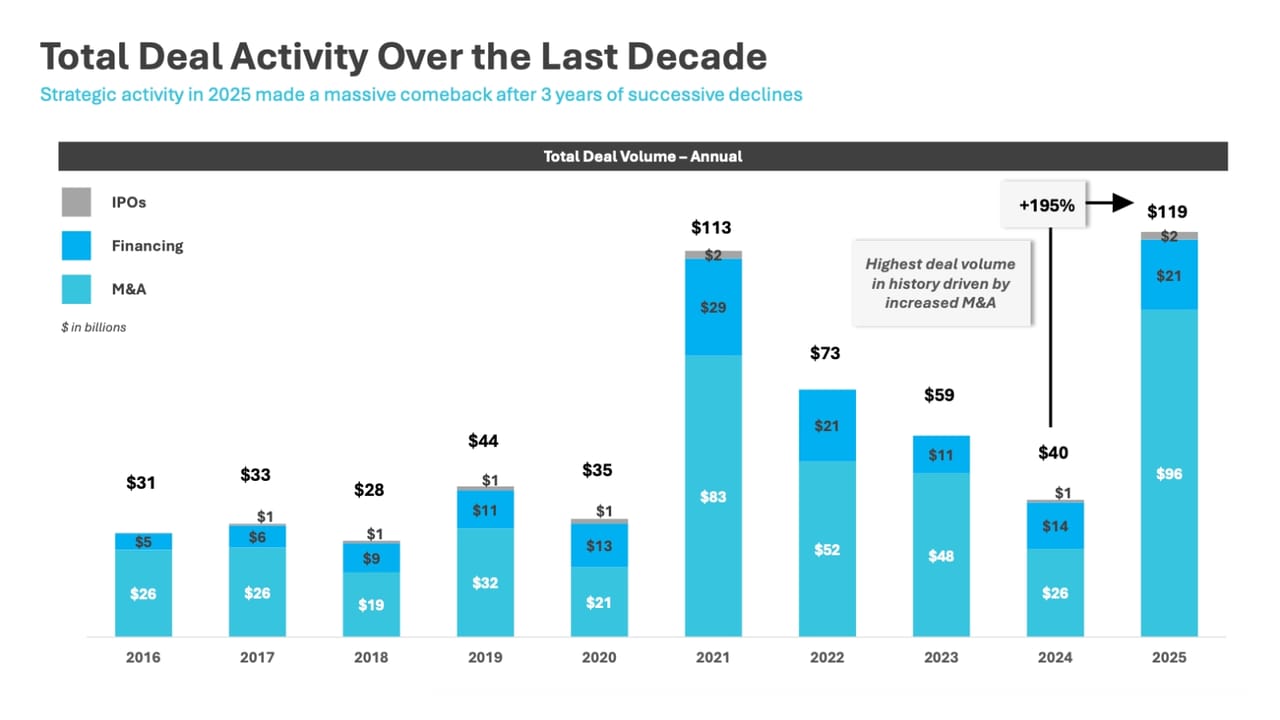
As Cybersecurity Firms Chase AI, VC Market Skyrockets
Investments in cybersecurity startups took off in 2025 as venture capital firms focused not just on AI-native tech but on talent as well.

Lazarus Group Picks a New Poison: Medusa Ransomware
The North Korean threat group also leveraged Comebacker backdoor, Blindingcan RAT, and info stealer Infohook in its recent attacks.

Attackers Now Need Just 29 Minutes to Own a Network
Credential misuse, AI tools, and security blind spots help attackers move through breached networks faster than ever, CrowdStrike finds.

Operation Red Card 2.0 Leads to 651 Arrests in Africa
In the latest operation targeting cybercrime groups, African law enforcement agencies cooperated with Interpol and cybersecurity firms to recover more than $4.3 million.
.jpg?width=1280&auto=webp&quality=80&disable=upscale)
'Richter Scale' Model Measures Magnitude of OT Cyber Incidents
ICS/OT experts have devised a scoring system for rating the severity and effects of cybersecurity events in operational technology environments.

Why 'Call This Number' TOAD Emails Beat Gateways
Attackers are bypassing email gateways through telephone-oriented attack delivery (TOAD), in which the only email payload is a phone number.

Malicious Next.js Repos Target Developers Via Fake Job Interviews
Linked to North Korean fake job-recruitment campaigns, the poisoned repositories are aimed at establishing persistent access to infected machines.

PCI Council Says Threats to Payments Systems Are Speeding Up
The PCI Security Standards Council experienced a record year in many regards, but its first annual report shows it needs to work even faster to stay ahead of attackers.
RAMP Forum Seizure Fractures Ransomware Ecosystem
Researchers suggest defenders monitor how these malicious groups re-form and leverage the useful threat intel to guide their next moves.

Flaws in Claude Code Put Developers' Machines at Risk
The vulnerabilities highlight a big drawback to integrating AI into software development workflows and the potential impact on supply chains.

Chinese Police Use ChatGPT to Smear Japan PM Takaichi
A Chinese keyboard warrior inadvertently leaked information about politically motivated influence operations through a ChatGPT account.
Cisco SD-WAN Zero-Day Under Exploitation for 3 Years
The maximum-severity vulnerability CVE-2026-20127 was exploited by an unknown but sophisticated threat actor who left very little evidence behind.